- meoward
- Posts
- 🐈 Twitter fired him – now he's blowing the whistle on their lack of security
🐈 Twitter fired him – now he's blowing the whistle on their lack of security
I read Mudge's 84-page whistleblower disclosure for you

Read time: 4 minutesChuckles: 14
Hi again, it's meoward – your inbox's weekly dose of security. This Sunday edition is brought to you by Ballmer's Windows 95 hype dance. 27 years later and Ballmer's still got the moves.
Short stack 🥞 this week:
⚖️ Mudge versus Twitter: I skipped all the news articles and went straight to the 84-page whistleblower disclosure. Don't have an hour? No worries, I've got the juicy stuff.
🍩 Sunday Snacks: encrypted zip files can have two correct passwords, a stager that pulls shellcode down over NTP, plus two breaches. Eat 'em with coffee!
Chop, chop. Look lively now.

OUR computer
Mudge Files Whistleblower Complaint against Twitter
Rewind sound effect. It's July 2020. Twitter has just experienced its worst breach ever. 130 high profile Twitter accounts were hijacked and used to promote a "double your Bitcoin" scam. The breach included accounts with huge followings like Barack Obama and Elon Musk.
The investigation that followed found that an estimated 1,500 employees at Twitter had access to internal admin tools that could reset Twitter user accounts. The attackers only had to successfully phish one of them. I like those odds.
Jack Dorsey, the CEO of Twitter (at the time) is like "I gotta fix this mess. I gotta hire the best." So what's he do? He hires Mudge.
So who is "Mudge"?
Rewind sound effect, but this time in VHS. It's May 1998. The 7 members of the hacker group L0pht are sitting before the US Senate. It's here that Mudge warns Congress of how common poor security practices are at major software companies. This is the infamous testimony where Mudge tells everyone that L0pht could cripple the Internet in 30 minutes. 🖐️🎤
Mudge is the guy in the center with long hair.

Hacker Jesus
Mudge joins Twitter, then gets the 🥾
It's November 2020. Mudge's hair is a lot shorter. It's 4 months after the massive breach at Twitter, and Jack Dorsey has just hired Mudge to tackle security at Twitter. "Be brutally honest."
But just a little over a year later, Mudge gets canned for "ineffective leadership and poor performance." Ouch.
And then this last week, CNN and The Washington Post drop the news that Mudge has filed a whistleblower complaint, and it doesn't look good for Twitter.
What's in the whistleblower complaint?
It's pretty obvious from the document that Mudge has issues with how he was treated at Twitter. And it's here that I'll say – I generally trust Mudge. He's a legend in the hacker community, and has nothing to gain from making this up. But let's trust Mudge for what Mudge knows best: security. Here's what he had to say:
Serious access control problems
🚩 Half of Twitter's 10k employees had privileged access to sensitive live production systems and user data in order to do their jobs.
🚩 In 2020 alone, Twitter had more than 40 security incidents, 70% of which were access control-related. These included 20 incidents defined as breaches; all but two of which were access control related.
🚩 The login system for Twitter's engineers was registering, on average, between 1,500 and 3,000 failed logins every day.

Lack of development or testing environments
🚩 Engineers built, tested, and developed new software using live customer data and deploying directly to production, leading to regular service disruptions.

Especially on Fridays.
Complete inability to track activity or delete data
🚩 No logging of who went into production, what they did, or what they changed.
🚩 No knowledge of where data lived or if it was critical. Only about 20% of Twitter's huge data sets were registered and managed.
🚩 Failure to properly delete user data when users requested their data be deleted. The reason? No one knew how the data was spread across different internal systems or how to account for it.
Knowing where all your data is – a complete mystery at Twitter!
Lack of endpoint visibility (for Twitter)
🚩 Over 30% of employee computers had software updates disabled, system firewalls turned off, and/or remote desktop enabled for non-approved purposes.
🚩 Employees intentionally installed spyware on their work laptops at the request of external organizations.
🚩 External people or organizations had more awareness of activity on some Twitter employee computers than Twitter itself.
Lack of data center redundancy
🚩 Lack of sufficient redundancies and procedures to recover from data center crashes, putting crucial user data at risk.
🚩 If all the centers went offline simultaneously, even briefly, Twitter was unsure if they could bring the service back up. Downtime estimates ranged from weeks of round-the-clock work, to permanent irreparable failure.
Vulnerabilities galore
Over half of Twitter's 500,000 servers ran:
🚩 outdated software that did not receive regular security updates and were missing basic security features like data encryption
🚩 non-compliant kernels or operating systems, and many unable to support encryption at rest
During log4j, Twitter had over 300 corporate systems and upwards of 10,000 services that might have been vulnerable. But Twitter could never determine its exposure to log4j because of the complete lack of visibility.

Twitter very strongly disagrees.
Snacks
🍿 [breach] Reset your Plex password (MPAA is buying password crackers).
🙃 [breach] Reset your LastPass password (and maybe switch password managers).
🗂 [blog] Encrypted zip files can have two correct passwords. Wait, what?
⏰ [tool] What time is it? It's time to find out if your blue team is monitoring their NTP traffic. Sandman is a stager that pulls down shellcode over NTP.

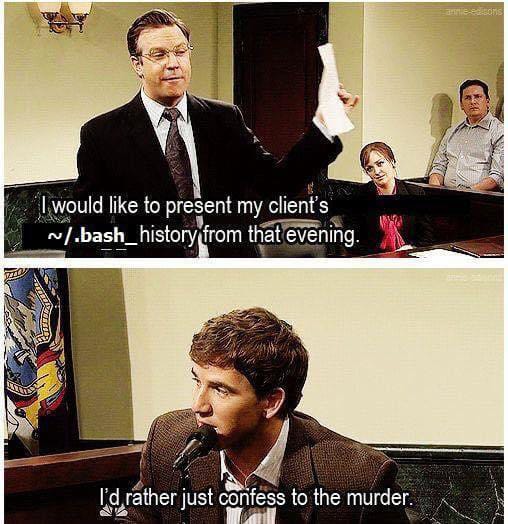
I love it when she wants to learn more about me.
How did you like today's email? |